Enhancing API Robustness: Stronger Password Policies and Type Safety in TypeScript
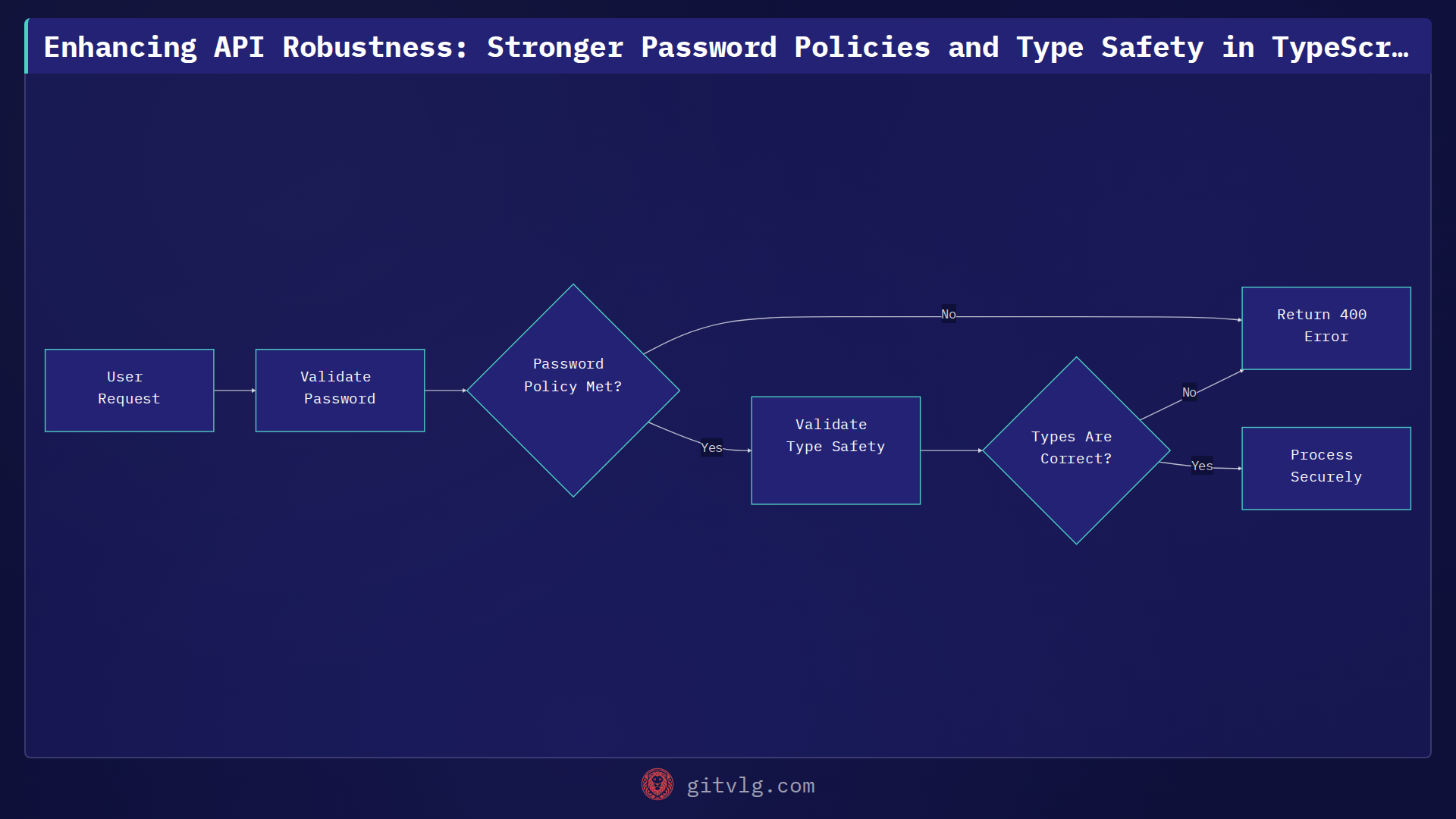
In the ims-api project, our focus is on building a robust and secure API platform. Recent updates have significantly bolstered our API's resilience by introducing stricter password policies and enhancing type safety practices. These changes are crucial for maintaining data integrity and reducing runtime errors, especially when dealing with sensitive user information.
The Need for Stronger Validation
Initial iterations of an API often prioritize functionality, sometimes leaving room for improvement in validation logic. For user authentication, a strong password policy is non-negotiable. Without it, the system is vulnerable to common attacks like brute-force attempts and dictionary attacks. Our recent work addressed this by enforcing a minimum password length, a foundational step in securing user accounts.
Implementing Secure Password Minimum Length with Zod
We leveraged Zod, a powerful TypeScript-first schema declaration and validation library, to enforce the new password policy. This ensures that any incoming password during user registration or update meets the minimum length requirement of 8 characters before it even reaches our database. This approach centralizes validation logic, making it easier to maintain and understand.
Here's a simplified example of how Zod can define a password schema with a minimum length:
import { z } from 'zod';
const passwordSchema = z.string()
.min(8, "Password must be at least 8 characters long")
.max(128, "Password cannot exceed 128 characters"); // Optional max length
interface UserCredentials {
username: string;
password: z.infer<typeof passwordSchema>;
}
// Example usage in an Express route handler
function registerUser(req: any, res: any) {
try {
const { username, password } = req.body;
const validatedPassword = passwordSchema.parse(password);
// Proceed with user creation using validatedPassword
res.status(200).json({ message: 'User registered successfully' });
} catch (error) {
if (error instanceof z.ZodError) {
return res.status(400).json({ errors: error.errors });
}
res.status(500).json({ message: 'Internal server error' });
}
}
This passwordSchema now explicitly dictates that any string validated against it must be at least 8 characters long, providing clear error messages if the condition isn't met.
Streamlining Validation Logic
Beyond new rules, maintaining clean and efficient code is paramount. We identified and removed duplicate validation checks, streamlining our codebase. Consolidating validation logic ensures consistency across the application and reduces the chance of discrepancies or overlooked edge cases. This also simplifies future updates to our validation rules.
Enhancing Type Safety: Moving Beyond Non-Null Assertions
A subtle yet significant improvement involved reviewing our TypeScript codebase to remove non-null assertion operators (!) from variables. While convenient, the non-null assertion operator tells the TypeScript compiler to trust that a value is not null or undefined, overriding its strict checks. If that assumption is wrong at runtime, it can lead to unexpected TypeErrors.
By removing these assertions, we're prompted to handle potential null or undefined values explicitly. This can involve using optional chaining (?.), nullish coalescing (??), or robust null checks, making our code more resilient to unexpected data states.
Consider this before-and-after:
Before (less safe):
interface Config {
settings?: { value: string };
}
function processConfig(config: Config) {
const settingValue = config.settings!.value; // Compiler trusts it's not null
console.log(settingValue);
}
// If config.settings is undefined, this will crash at runtime
processConfig({});
After (more robust):
interface Config {
settings?: { value: string };
}
function processConfig(config: Config) {
// Safely access with optional chaining and nullish coalescing
const settingValue = config.settings?.value ?? 'default';
console.log(settingValue);
}
// Handles undefined settings gracefully
processConfig({}); // Outputs: default
This small change encourages developers to write more defensive code, leading to fewer runtime errors and a more predictable application.
Actionable Takeaway
Always prioritize explicit validation and type safety. Leverage libraries like Zod for defining clear, centralized schemas, especially for critical data like passwords. Furthermore, consciously avoid the non-null assertion operator (!) in TypeScript when possible, opting instead for safer null handling strategies to prevent runtime exceptions and improve overall code robustness. These practices are fundamental to building secure and maintainable APIs.
Generated with Gitvlg.com