Hardening Supabase Functions: The Path to Secure Database Operations
Even the most robust backend-as-a-service platforms, like Supabase, require diligent attention to security, especially when interacting directly with your database via custom functions. A small misstep in function design can open up critical vulnerabilities, exposing data or allowing unauthorized operations. The recent work on the ims-platform/ims-api project highlights precisely this – a critical focus on strengthening database function security and maintaining a clean, secure codebase.
Understanding Function Security in PostgreSQL
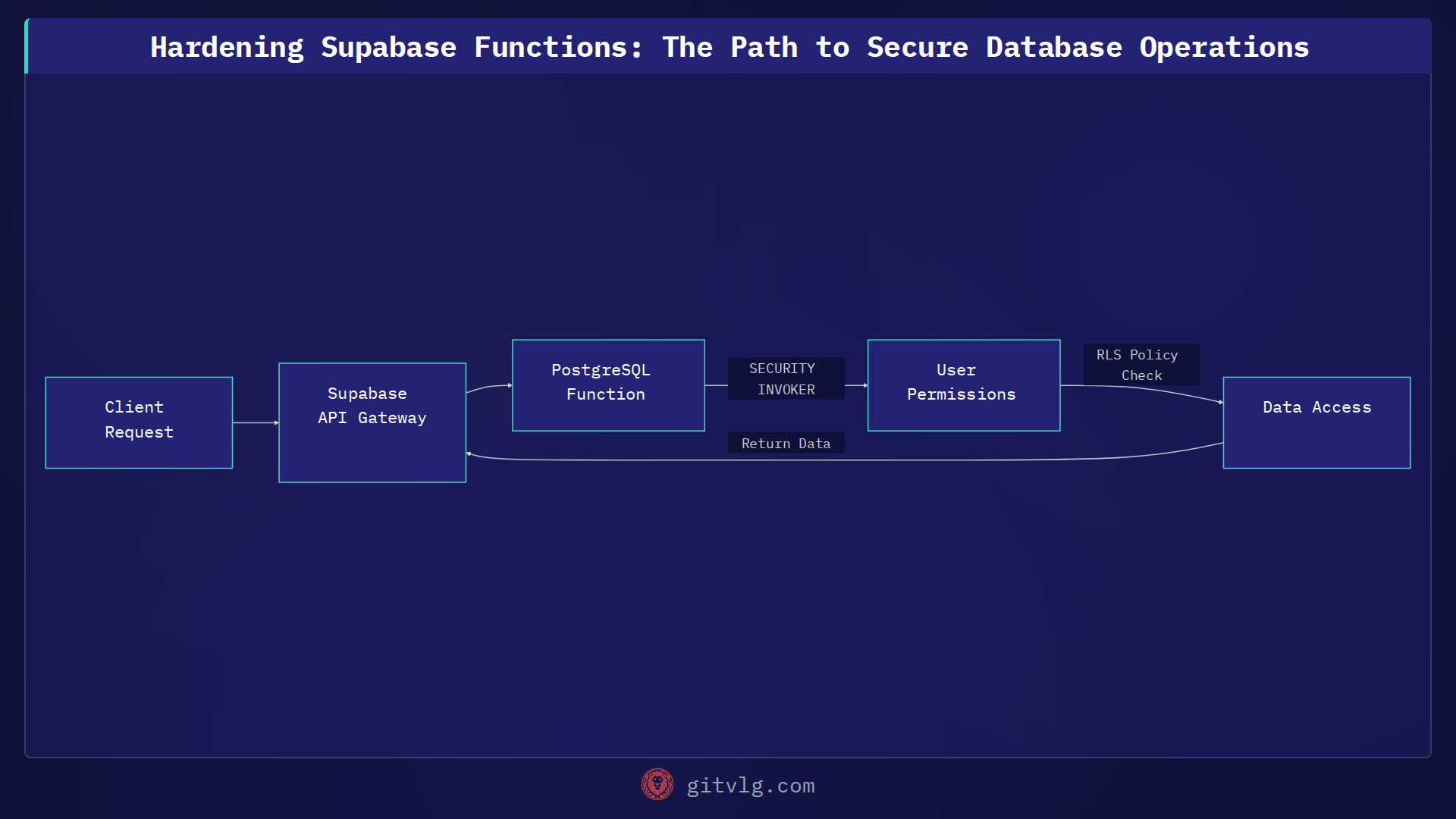
When you create functions in PostgreSQL (which Supabase leverages), you define not just what they do, but also how they execute in terms of privileges. This is where SECURITY DEFINER and SECURITY INVOKER come into play, a distinction that often determines the robustness of your application's data layer.
A function marked SECURITY DEFINER executes with the privileges of the user who defined it. While powerful for tasks requiring elevated permissions (e.g., modifying system catalogs), it's also a common source of security bypasses if not meticulously handled. Such functions can unwittingly ignore Row-Level Security (RLS) policies, allowing a low-privileged user to perform high-privileged actions.
Conversely, a SECURITY INVOKER function runs with the privileges of the user who calls it. This is generally the safer default, as it respects all RLS policies and permissions associated with the current session's user. It acts as an extension of the calling user's permissions, not an escalation.
The ims-api Security Fix
In ims-api, the recent fix involved ensuring that critical database functions operate under the principle of least privilege. By reviewing and adjusting function definitions, particularly transitioning functions that don't explicitly require elevated privileges to SECURITY INVOKER, we've significantly reduced the attack surface. This change means that every operation performed by these functions is now properly constrained by the calling user's permissions and any applicable RLS policies.
Accompanying this security enhancement was a focused effort to remove outdated or redundant 'snippets' from the codebase. This cleanup is more than just good hygiene; it removes potentially insecure or unused code paths that could become liabilities in the future, simplifying auditing and reducing cognitive load for developers.
Illustrative Code Example: Securing a Data Retrieval Function
Consider a simple function to retrieve user settings. An insecure version might look like this, potentially bypassing RLS:
CREATE FUNCTION get_user_settings_insecure(user_id uuid) RETURNS SETOF app_config AS $$
BEGIN
RETURN QUERY SELECT * FROM app_config WHERE user_id = get_user_settings_insecure.user_id;
END;
$$ LANGUAGE plpgsql SECURITY DEFINER;
This function, if called by a user, would execute with the privileges of the user who created it (e.g., postgres), potentially revealing settings for other users, even if RLS is enabled for app_config.
The secure approach ensures the function respects the caller's context:
CREATE FUNCTION get_user_settings_secure() RETURNS SETOF app_config AS $$
BEGIN
RETURN QUERY SELECT * FROM app_config WHERE user_id = auth.uid();
END;
$$ LANGUAGE plpgsql SECURITY INVOKER;
In the get_user_settings_secure function, we've removed the user_id parameter and instead rely on auth.uid() (a common Supabase function to get the current user's ID) and explicitly defined it as SECURITY INVOKER. Now, this function will only return app_config rows that the auth.uid() (the current user) is authorized to see, fully respecting RLS policies.
Key Takeaways for Secure Supabase Development
- Prioritize
SECURITY INVOKER: For most application-facing functions,SECURITY INVOKERis the correct and safest default. Only useSECURITY DEFINERwhen absolutely necessary, and always pair it with explicit privilege checks within the function. - Leverage RLS: Supabase's Row-Level Security is a powerful defense. Ensure your functions work with RLS, not around it.
- Regular Code Audits: Periodically review your database functions and backend code for potential security flaws and to remove outdated or unnecessary code. A clean codebase is a secure codebase.
By diligently applying these principles, developers can ensure that their Supabase-powered applications remain robust and resistant to common database-level vulnerabilities.
Generated with Gitvlg.com